AI Identity Fabrication: The Rise of Fake Online Personas
Across social media, dating apps, forums, and comment sections, a quiet threat is growing. AI identity fabrication, the use of artificial intelligence to create convincing fake online personas, is reshaping how trust and deception work on the internet. Whether you’re scrolling Instagram, swiping on a dating app, or reading reviews, you may have already encountered a persona that never existed.
What Is AI Identity Fabrication?

AI identity fabrication refers to the use of AI tools to generate fake but realistic online identities. These synthetic personas typically combine AI-generated profile photos, machine-written bios, and automated behavior to mimic real human users.
Common Types of Fake AI Personas
- Synthetic social media accounts: Profiles with AI-generated faces (via tools like GANs), believable backstories, and consistent posting behavior.
- AI chatbots posing as humans: Used in romance scams, customer manipulation, or political influence campaigns.
- Fake reviewers: AI-written product or service reviews designed to appear authentic.
- Deepfake-linked personas: Identities supported by AI-generated video or voice to add a layer of believability.
These aren’t just bots with obvious tells anymore. Modern AI identity creation produces personas that can pass casual human scrutiny.
How AI Identity Fabrication Works
Understanding the mechanics helps you recognize it.
Generative AI Tools Behind Fake Personas
Fabricated online identities are typically built using a combination of:
- GAN-generated profile photos: Tools like ThisPersonDoesNotExist.com use Generative Adversarial Networks to create photorealistic faces of people who don’t exist.
- Large language models (LLMs): AI like GPT-based tools generate written content: bios, posts, messages, and comments that read naturally.
- Automated account management tools: Scripts or platforms that mimic human posting schedules, interactions, and engagement patterns.
- Scraped personal data: Real user data is sometimes blended with AI-generated content to make fake personas harder to detect.
The result is a digital identity that looks lived-in, consistent, and human.
Why AI Fake Personas Are a Growing Threat
Social Engineering and Scams
Fake AI personas are increasingly used in social engineering attacks, gaining a victim’s trust before extracting money, personal data, or login credentials. Romance scams powered by AI chatbots are a well-documented example, with victims losing thousands of dollars to personas that exist entirely in software.
Misinformation and Influence Campaigns
Networks of AI-fabricated accounts, often called astroturfing bots, are deployed to push narratives, manipulate trending topics, or manufacture fake public consensus. This is a direct threat to how everyday users perceive news and online opinion.
Identity Theft and Impersonation
AI identity fabrication is also used to impersonate real individuals, cloning their likeness, writing style, or voice to commit fraud or damage reputations.
How to Spot a Fake AI-Generated Persona
Warning Signs on Social Media
- Flawless, symmetrical profile photos: AI-generated faces often have perfect skin, unusual backgrounds, or asymmetrical earrings and eyes on close inspection.
- Vague or generic bio: Fake personas often list broad interests with no verifiable specifics.
- No tagged photos or real-world connections: Real users accumulate organic tags, group photos, and friend interactions over time.
- Inconsistent posting history: Accounts with thousands of posts but a recent creation date are suspicious.
- Overly polished writing: Responses that are always grammatically perfect and eerily balanced may be LLM-generated.
Tools You Can Use to Verify
- Reverse image search: Right-click any profile photo and search Google Images or TinEye. If the image appears nowhere else, it may be AI-generated.
- Hive Moderation or Illuminarty: Free online tools that can detect AI-generated images with reasonable accuracy.
- Social media platform reporting: Both Facebook and Instagram have tools to report suspected fake accounts under their “It’s a fake account” category.
How to Protect Yourself From AI Identity Fabrication
Strengthen Your Own Digital Identity
One underappreciated risk: your own photos and data can be scraped and used to train or build fake personas. Here’s how to limit your exposure:
- Set your social media profiles to private or friends-only.
- Avoid posting high-resolution face photos publicly.
- Regularly audit which apps have access to your photos and personal data.
On Windows 10/11: Protect Your Privacy From Unwanted Data Access
If you use a Windows PC, apps installed on your system may have access to your camera, microphone, and location data that could be compromised and misused. Here’s how to review and restrict app permissions:
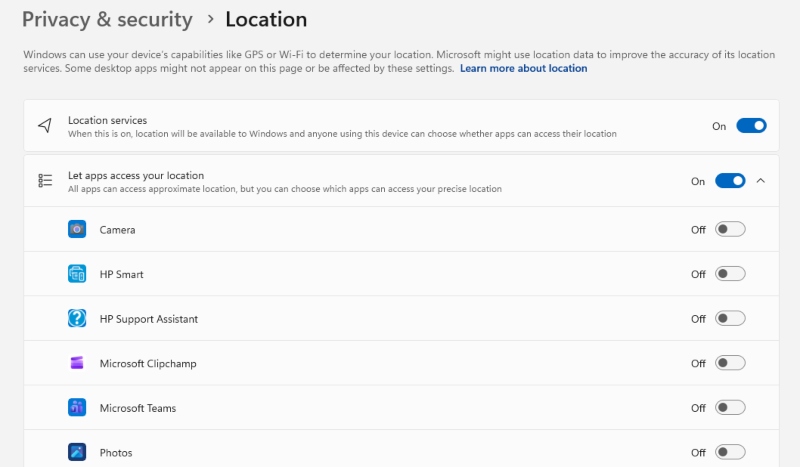
1: Open Windows Settings Press Windows + I to open the Settings app.
2: Navigate to Privacy & Security Click on Privacy & security in the left-hand sidebar.
3: Review App Permissions. Scroll down to the App permissions section. Click each category — Camera, Microphone, Location — to see which apps have access.
4: Revoke Unnecessary Access. Toggle off any app that doesn’t need access to that sensor. For example, a note-taking app doesn’t need your camera.
5: Disable Access System-Wide (Optional) At the top of each permission page, you’ll see a master toggle (e.g., “Let apps access your camera”). Turn this off to block all apps from accessing that resource system-wide.
6: Check Desktop App Permissions. Note that traditional desktop apps (not from the Microsoft Store) won’t appear in this list. Be cautious about what software you install and always download from verified sources.
Strengthen Your PC Security with Fortect

Locking down app permissions is a solid first step, but it doesn’t cover every angle. Threats tied to AI identity fabrication can also arrive through malicious software, fake apps, phishing-linked downloads, or spyware designed to harvest your personal data and photos for use in synthetic personas. That’s where dedicated protection matters.
Fortect delivers advanced real-time malware protection for Windows users. It automatically scans your PC for traditional and emerging threats, including AI identity fabrication-related malware, eliminates them safely, and restores damaged system files for improved performance. Its smart threat-detection engine monitors suspicious activity and alerts you before harmful actions can take place, helping keep your device secure and running efficiently.
Download and install Fortect today and secure your systems from AI identity fabrication.
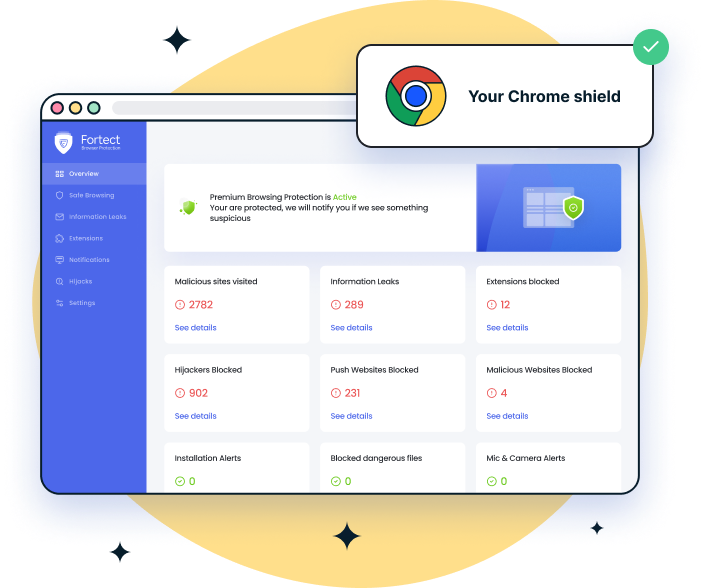
For Chrome users, a browser protection tool can help reduce the risk of AI identity fabrication–driven phishing scams. Fortect Browsing Protection is an easy-to-use Chrome extension that adds an extra layer of security by blocking dangerous websites before they load, warning you about suspicious pages often used in phishing attempts, and removing harmful extensions that could expose your personal data.
What Platforms Are Doing About It
Major platforms including Meta, X (formerly Twitter), and LinkedIn have invested in AI detection systems to flag and remove fabricated accounts. However, detection consistently lags behind creation. As AI tools become cheaper and more accessible, the volume of fake persona creation outpaces automated moderation.
The responsibility increasingly falls on users to stay skeptical and informed.
Conclusion
AI identity fabrication is no longer a fringe concern, it’s a mainstream digital safety issue. Fake personas are used to scam, manipulate, and deceive ordinary people every day. By understanding how synthetic identities are built, learning to spot the warning signs, and taking practical steps to protect your own data, you can navigate online spaces with significantly more confidence.
Stay skeptical of new connections, verify before you trust, and remember: if a profile feels too perfect, it might not be a person at all.



